Integration of EST4 with newer detection devices
In today’s technologically advanced world, the integration of advanced detection devices with existing systems has become crucial for ensuring safety and security. One such system that has gained prominence is the EST4. This article explores the basics of EST4, the evolution of detection devices, the process of integrating EST4 with detection devices, the benefits, and future trends in this field.
Understanding the Basics of EST4
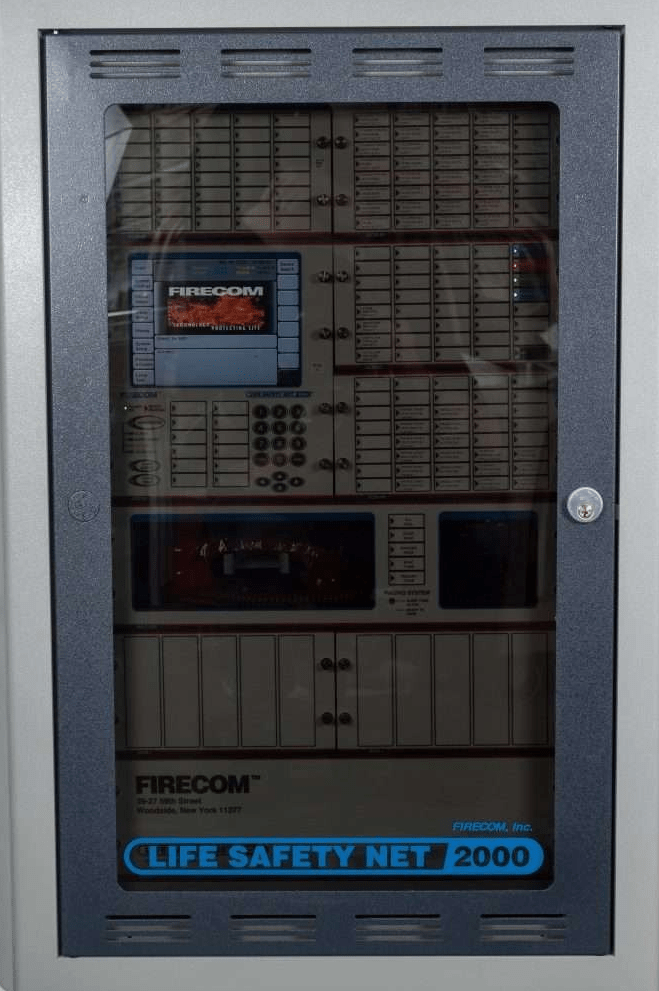
EST4, short for Enhanced Security Technology 4, is a robust and state-of-the-art security system designed to provide reliable detection and rapid response in various applications. This advanced system offers a comprehensive range of features, making it highly versatile and adaptable to different environments.
With its user-friendly interface, the EST4 allows users to easily monitor and control their security systems, ensuring effective management of alarms, sensors, and other devices. Its sophisticated architecture and advanced algorithms enable efficient detection and analysis of potential threats, enhancing the overall security infrastructure.
EST4 is more than just a security system. It is a cutting-edge solution that combines advanced technology with intelligent features to create a comprehensive security ecosystem. Let’s dive deeper into the functionality and use of EST4.
The Functionality and Use of EST4
The functionality of the EST4 revolves around its ability to integrate seamlessly with various detection devices, such as motion sensors, CCTV cameras, access control systems, and more. This integration enables real-time monitoring, event tracking, and data analysis, providing a holistic security solution.
Imagine a scenario where an unauthorized person tries to gain access to a restricted area in a commercial building. With EST4, the motion sensors would detect the movement and trigger an alarm. Simultaneously, the CCTV cameras would start recording the incident, providing valuable evidence for further investigation. The access control system would also deny entry, ensuring that only authorized personnel can access the area.
The EST4 also offers a wide range of applications, including but not limited to commercial buildings, industrial facilities, healthcare institutions, and educational campuses. Its versatility ensures that it can be customized to meet the specific security needs of different industries.
In a healthcare institution, for example, the EST4 can be integrated with patient monitoring systems to ensure the safety and well-being of patients. It can detect abnormal activities, such as patients leaving their beds without assistance, and immediately alert the healthcare staff, enabling prompt response and preventing potential accidents.
Whether it’s securing a large industrial facility or protecting a small retail store, EST4 provides a scalable and adaptable solution that can be tailored to fit any security requirement.
Key Features of EST4
The key features of EST4 set it apart from conventional security systems. Firstly, its advanced analytics capabilities enable intelligent video surveillance and alarm verification, reducing false alarms and improving response times. By analyzing video footage in real-time, the system can differentiate between actual threats and harmless events, such as a stray animal passing by, ensuring that security personnel can focus on genuine emergencies.
Additionally, its scalability allows for easy expansion and integration with other security systems, ensuring future-proofing. As security needs evolve and grow, EST4 can seamlessly integrate with new technologies and devices, providing a flexible and scalable solution that can adapt to changing requirements.
Moreover, EST4 provides remote access and control, allowing users to monitor their security infrastructure from anywhere at any time. This feature is particularly beneficial for multi-site organizations, providing centralized management and enhanced situational awareness. Security managers can access live video feeds, receive real-time alerts, and make informed decisions, even when they are not physically present at the site.
EST4 is not just a security system; it is a comprehensive security solution that combines cutting-edge technology, advanced analytics, and remote accessibility to provide unparalleled protection and peace of mind.
The Evolution of Detection Devices
The integration of EST4 with newer detection devices would not be possible without the continuous advancements in detection technology. Over the years, detection devices have undergone significant transformations, leading to improved accuracy, reliability, and functionality.
One of the key factors driving the evolution of detection devices is the constant demand for enhanced security measures. As threats become more sophisticated, detection technology must keep up to ensure effective protection. This has led to the development of a wide range of innovative sensors and devices that are capable of detecting various types of threats.
The Progression of Detection Technology
The progression of detection technology has paved the way for more sophisticated and efficient sensors. From traditional wired sensors to wireless and IoT-enabled devices, the industry has witnessed a paradigm shift. This shift has not only improved the ease of installation but also expanded the coverage area of detection systems.
With the advent of wireless technology, detection devices can now be placed in areas that were previously difficult to reach. This includes remote locations, outdoor spaces, and even underground facilities. The ability to deploy sensors in these areas greatly enhances the overall security infrastructure.
Moreover, the use of advanced algorithms, machine learning, and AI has further revolutionized the way detection devices operate. These technologies enable devices to analyze vast amounts of data in real-time, allowing for quicker and more accurate threat detection. By continuously learning and adapting, these devices can identify patterns and anomalies that may indicate a potential security breach.
Today’s detection devices are equipped with intelligent features, such as adaptive learning and behavior recognition, enabling them to differentiate between genuine threats and false alarms. This reduces the occurrence of unnecessary disruptions and ensures that security personnel can focus their attention on real threats.
Additionally, integration with cloud-based platforms has facilitated remote monitoring and real-time data analysis, significantly enhancing overall security. With cloud connectivity, detection devices can transmit data to a centralized system where it can be analyzed and acted upon. This allows for proactive security measures and faster response times.
Characteristics of Newer Detection Devices
Newer detection devices boast several characteristics that make them suitable for integration with EST4. These devices are designed to be highly sensitive, ensuring accurate detection while minimizing the occurrence of false positives and negatives.
Their ability to detect anomalies and patterns in data enables proactive prevention of security breaches. By continuously monitoring and analyzing data, these devices can identify unusual behavior or events that may indicate a potential threat. This early detection allows security personnel to take appropriate action before a situation escalates.
Furthermore, improved communication protocols and interoperability features enable seamless integration with other security systems, promoting a unified approach. This compatibility ensures that the detected events and alarms are relayed and responded to effectively, enhancing the overall security ecosystem.
In conclusion, the evolution of detection devices has been driven by the need for enhanced security measures and advancements in technology. From wired to wireless, and from basic sensors to intelligent devices, the industry has made significant progress in improving the accuracy, reliability, and functionality of detection systems. With the integration of EST4, these newer detection devices can further enhance security measures and provide a comprehensive solution for various industries and applications.
The Process of Integrating EST4 with Detection Devices
The integration process between EST4 and detection devices involves several considerations and steps to ensure optimal functionality and performance.
Integrating EST4 with detection devices is a complex and critical task that requires careful planning and execution. This process involves various stages, from pre-integration considerations to the step-by-step integration procedure. By following these steps diligently, security professionals can ensure a seamless integration that enhances the overall security infrastructure.
Pre-Integration Considerations
Prior to integration, it is essential to conduct a thorough assessment of the existing security infrastructure and requirements. This assessment involves identifying compatibility issues, evaluating the need for hardware or software upgrades, and establishing communication protocols.
During this stage, security professionals collaborate closely with system integrators and installers to gather all the necessary information. They analyze the existing infrastructure, including the network architecture, power supply, and connectivity options. By understanding the current setup, they can determine the best approach for integrating EST4 with the detection devices.
Furthermore, a comprehensive integration plan should be drafted, detailing the timeline, scope, and resources required for a successful integration. Cooperation and collaboration between security professionals, installers, and system integrators are crucial in this phase to ensure a smooth transition.
Once the pre-integration considerations are addressed, the actual integration process can begin.
Step-by-Step Integration Procedure
The integration procedure typically involves the following steps:
- System Configuration: EST4 and the detection devices are configured to establish communication and synchronization between them. This step includes setting up IP addresses, network protocols, and ensuring compatibility between different systems.
- Device Configuration: Each detection device is configured to communicate with the EST4 system, including setting up event triggers and defining alarm thresholds. This step requires a deep understanding of the detection devices’ capabilities and functionalities.
- Physical Installation: The detection devices are installed at strategic locations, ensuring maximum coverage and optimal detection capabilities. This step involves careful planning to identify the areas that require enhanced security measures, such as entrances, high-risk zones, and critical infrastructure.
- Data Integration: The data from detection devices, such as video feeds, sensor readings, and access control logs, are integrated into the EST4 system for centralized monitoring and analysis. This integration allows security professionals to have a comprehensive view of the security landscape, enabling them to respond swiftly to any potential threats.
- Testing and Calibration: Once the integration is complete, thorough testing and calibration are conducted to verify the accuracy and reliability of the integrated system. This step involves simulating various scenarios, such as intrusion attempts or fire incidents, to ensure that the system responds appropriately.
During the testing phase, security professionals work closely with system integrators and installers to fine-tune the system settings and address any issues that may arise. This iterative process ensures that the integrated system meets the specific security requirements of the facility.
Once the testing and calibration are successfully completed, the integrated system is ready for deployment, providing enhanced security and peace of mind for the facility’s occupants.
Benefits of EST4 and Detection Device Integration
The integration of EST4 with newer detection devices offers a plethora of benefits, transforming the security landscape.
EST4, a cutting-edge security technology, when integrated with advanced detection devices, revolutionizes the way organizations approach security. This integration brings forth a host of advantages that enhance performance, efficiency, and overall effectiveness in security operations.
Enhanced Performance and Efficiency
By integrating EST4 with detection devices, organizations can achieve enhanced performance and efficiency in their security operations. The combination of advanced analytics, real-time monitoring, and centralized management enables faster threat detection and response.
With EST4’s advanced analytics capabilities, security personnel gain access to powerful tools that can analyze vast amounts of data in real-time. This allows for the identification of potential security risks and threats with greater accuracy and speed. The integration also facilitates the seamless sharing of information between EST4 and detection devices, enabling a more comprehensive and proactive approach to security.
Moreover, the integration allows for automation of various security processes, reducing the burden on security personnel and minimizing human errors. Routine tasks such as access control, video surveillance, and alarm management can be streamlined and automated, freeing up valuable time for security teams to focus on critical situations. This streamlined approach improves overall efficiency, ensuring a proactive and effective response to potential security risks.
Potential Challenges and Solutions
While integrating EST4 with detection devices brings numerous benefits, there can be challenges associated with compatibility issues, scalability, and system complexity. However, these challenges can be mitigated through careful planning, thorough testing, and partnering with experienced system integrators.
Compatibility issues may arise when integrating EST4 with different detection devices from various manufacturers. However, by working closely with experienced system integrators, organizations can ensure that the integration is seamless and all components work together harmoniously. Thorough testing and validation of the integrated system before deployment can help identify and resolve any compatibility issues early on.
Scalability is another consideration when integrating EST4 with detection devices. As organizations grow and expand, the system should be able to accommodate increased security requirements. By selecting scalable detection devices and designing a flexible architecture, organizations can future-proof their security infrastructure.
System complexity can also be a challenge, especially when integrating multiple security systems into one cohesive solution. However, with careful planning and collaboration between security experts and system integrators, organizations can design an integrated system that is easy to manage and operate. Regular system maintenance and software updates are essential to ensure continuous compatibility and optimal performance.
Additionally, providing comprehensive training to security personnel will enable them to effectively utilize the integrated system and address any issues that may arise. Training programs should cover not only the technical aspects of the system but also best practices for leveraging its capabilities to enhance security operations.
Future Trends in EST4 and Detection Device Integration
The field of EST4 and detection device integration is poised to witness several exciting developments in the near future.
As technology continues to advance, the integration process is expected to become even more seamless and efficient. Smarter algorithms, improved connectivity, and the use of edge computing are likely to enhance the capabilities of detection devices, enabling real-time threat mitigation.
One of the predicted developments in technology is the integration of machine learning and AI algorithms into the EST4 system. This integration will enable more accurate threat prediction and proactive security measures. By analyzing vast amounts of data and identifying patterns, the system will be able to anticipate potential threats and take appropriate actions to prevent them. This advancement will revolutionize the way security operations are conducted and redefine the standards of safety and protection.
Furthermore, the implications of these developments for users and industries are significant. As the integration of EST4 with detection devices becomes more prevalent, users and industries will experience a paradigm shift in their security strategies. The seamless integration and interoperability between systems will enable a comprehensive approach to security, reducing vulnerabilities and minimizing risks.
Industries such as banking, healthcare, transportation, and retail will benefit immensely from the integration of EST4 with detection devices. In the banking sector, for example, the integration will provide enhanced protection against fraud and unauthorized access to sensitive information. In healthcare, the integration will ensure the safety and privacy of patients’ data and enable real-time monitoring of critical medical equipment. In transportation, the integration will enhance the security of passengers and cargo, reducing the risk of theft or terrorism. In retail, the integration will help prevent shoplifting and ensure a safe shopping environment for customers and employees.
The increased reliability and effectiveness of security systems will instill confidence and peace of mind among users, enabling them to focus on their core operations without compromising safety. Organizations will be able to allocate their resources more efficiently, knowing that their security infrastructure is robust and future-proof.
In conclusion, the integration of EST4 with newer detection devices marks a significant milestone in the realm of security systems. As technology continues to progress, organizations must embrace these developments to ensure robust and efficient security measures. The advantages of integrating EST4 with detection devices are vast, ranging from enhanced performance to future-proofing the security infrastructure. With careful planning, seamless integration, and proactive maintenance, organizations can achieve an unparalleled level of security, keeping pace with the dynamic landscape of threats and vulnerabilities.